
The first approach used by Cisco’s Talos Threat Intelligence team was that of TLS certificate matching. With this approach the self signed certificate that is used by their dark web website is cross referenced with indexed clear web certificates to see if they appear on any sites found on the public internet.
Normally ransomware sites do not use a certificate due to needing to include the certificate from the issuing authority which in turn can be used as an identifier.
Some of the identifying information that certificates include are a unique serial number and cryptographic key. This is traceable if its reused on other web properties.
The reason for using the dark web is to remain anonymous. Identity attestation provided by certificates can help to pinpoint the threat actor behind the website.
There is the possibility that Ransomware Groups use certificates on their sites on the dark web to make victims feel like they are operating in a secure environment and to give their operations legitimacy.
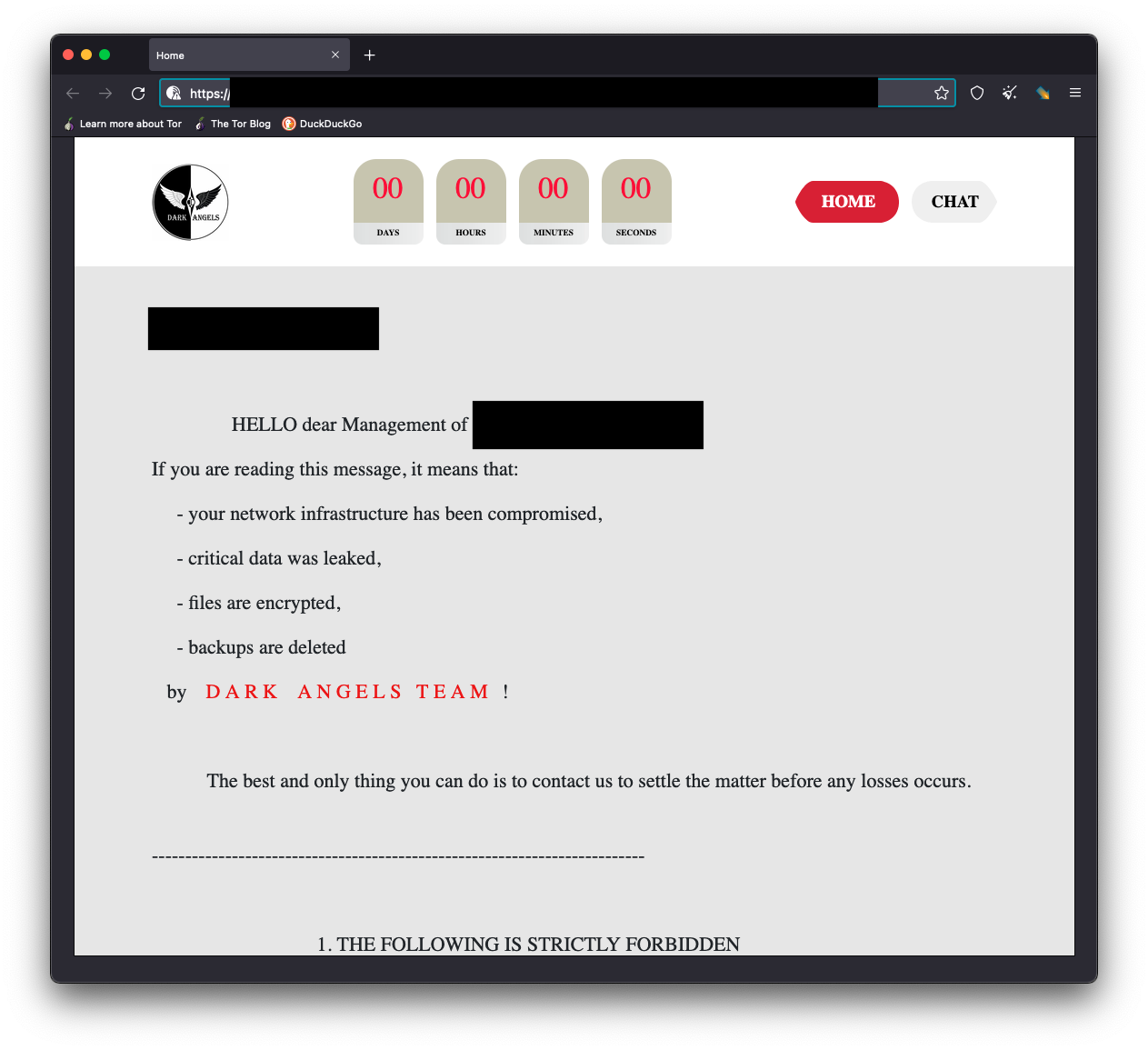
DarkAngels
De-anonymization
If we visit the host on the public web using the IP address we discover that the same information as the masked dark web site is visible.
You are also able to verify the TLS certificate serial number. This shows that it is the same even on the site hosted on the TOR network.
With this information the Talos team was able to determine that the DarkAngels are using a TLS page to host their victim interactions page on the TOR Network as well as the clear web. As a result of this we are able to determine which hosting provider is being used.
As a result of the de-anonymization the Talos Team were able to see a number of A records in DNS with the associated ip address for the site found on the surface web.
- login.myob[.]link
- myob[.]live
- www.myob[.]live
- Login.myob[.]live
In order to maintain their anonymous operations, Talos were able to determine the above domains were registered using a privacy domain registration proxy service.
Talos also noted that as of 22nd May 2022 the login.myob[.]link Domain was still resolvable to the previously mentioned IP address of the DarkAngles that is using to host their infrastructure on.
Private keys and login portals exposed
It has also been observed that there is a public facing .env file which exposes the connection string information for their database. This is most likely that holds all chat logs. What come as a surprise is that it leaks the APP_SECRET key.
As a result of this we can see that the threat actor is using a PHP framework for creating web applications called Symfony.
One is also able to see that the threat actor has a login page for a service that it has running on its website.
Snatch Ransomware
The Snatch ransomware group also use the TOR network to hide their services as well as use a certificate on their site which hosts their write-ups and data leaks.
What is difference is that they post a clear web link on their main page which points to snatch[.]press on the surface web.
It is also important to note that Snatch are able to pin point the hosting provider that is being used, but the URI rotates frequently, almost on a daily basis, based on telemetry from Cisco Umbrella.
With this information we have so far, we only have the partial story.
If we use nslookup, we can see that the IP address for the URI snatch[.]press resolves to 80.66.64.91.
If we then point our browser to the above mentioned IP address, we get a connection failure response.
If we use the same certificate matching technique previously mentioned and the hxxps://snatch[.]press we see that this domain is also associated with 2 additional IP addresses, with one of the 2 being the address where the site is actually hosted.
The Talos team was also able to determine with the two IP addresses and certificate, that it belongs to a Swedish hosting provider.
Visiting the ip address 91.236.116.21 it confirms the location that it is hosted at.
Leave a Reply