Workstation & Enterprise Server Backups
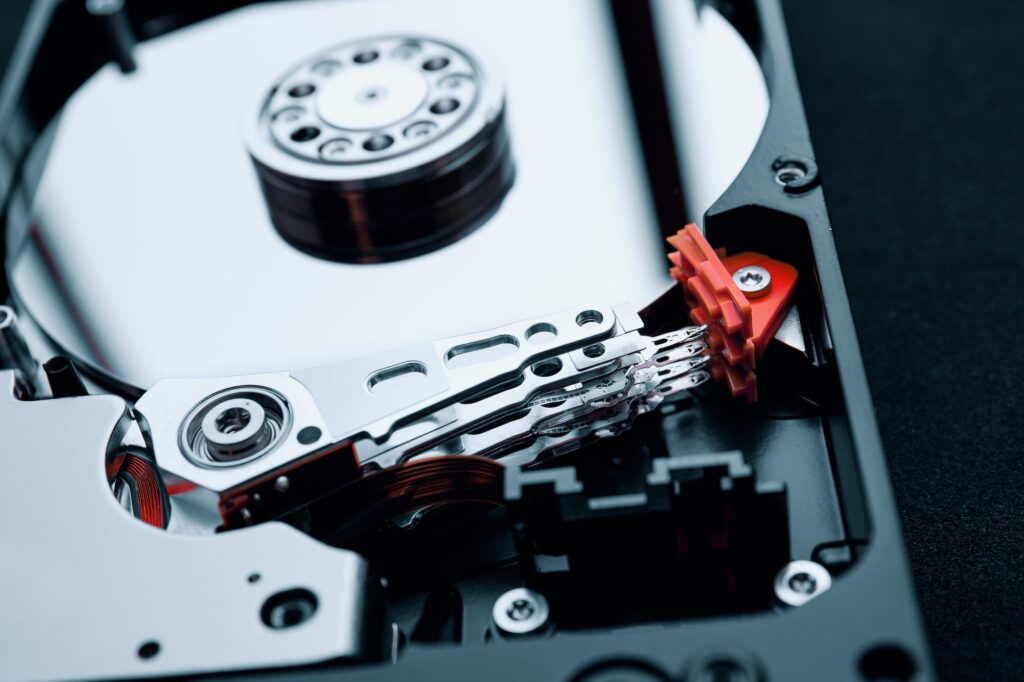
In the age of Ransomware as a Service, and the increase of these types of attacks, having backups is essential. Not just backups onsite, but also offsite.
When a ransomware attack occurs, onsite backups are usually the first that are deleted and backup software is disabled. This leads to the victim either being forced to pay the ransom that they are being asked for even though it would not guarantee the decryption of the encrypted data.
Here at EagleEyeT, we can provide you with a cost effective, secure offsite backup solution that you can use to cover both your servers and workstation’s.
Reach out to us on [email protected] for a free quote or consultation.
Recent Posts
- Safari’s Leap Towards Enhanced Privacy: Apple’s Latest Update
- The Ultimate SFTP FAQ Guide: Enhancing File Transfer Security
- Navigating the Digital Threat Landscape: Your Cybersecurity FAQs Answered
- Navigating the Cybersecurity Maze: Azure HDInsight’s XSS Vulnerabilities Unveiled
- Unveiling the Future of Software Testing: The Power of AI
Recent Comments
Categories
- AI Regulations
- Alerts
- Artificial Intelligence (AI)
- Compliance
- Cyber Awareness Month
- Cyber Insurance
- Cybersecurity
- Cyberwarfare
- E-Signatures
- FAQ
- Glossary
- Hardware
- Infrastructure
- IT News
- Machine Learning (ML)
- Opinion
- Podcast
- Quantum Computing
- Reviews
- Social Media
- Software Testing
- Statistics
- Statistics
- Supply Chain Attack
- Sustainability
- Technology
- Tutorial
- Uncategorized
- Zero Trust